Reading Mugs and Keeping Secrets
Hey Folks, here is a quick update on Mugsy's RFID functionality and some cool info security news.
Making Modules
Some of Mugsy's more interesting functionality has existed mostly as hacks and proofs of concepts. So one of the major development projects is taking these bits and scripts and cleaning them up and wrapping them up into a module. Each module is a self contained unit with it's own API endpoint. This means that any module can easily be accessed and controlled using lots of different programming languages and methods.
The RFID Mug Reader is a great example of this. It was initially a script that ran standalone on an Arduino. The RFID hardware scanned the mug, grabbed the mug ID and the Arduino then sent it over serial to the Raspberry Pi. A python script on the PI was listening for the ID and once received, it would query the database for that users favorite brew settings. Boom, easy peasy.
So when I wanted to show off RFID functionality, I would run mugReader.py and it would put all these pieces in motion. Great for demos but useless for a runtime. Making the module is how we turn a hack like this into a robust and usable feature.
So what makes a module a module? Not much actually! Obviously the code needs to be cleaned up, but the important part is simply exposing and declaring how a module communicates. Each module has a config file that tells the Mugsy runtime what is accessible and how to access it. In this specific case, what is accessible is a Mug ID and it's accessed from the Arduino, over a serial address. That's really easy peasy.
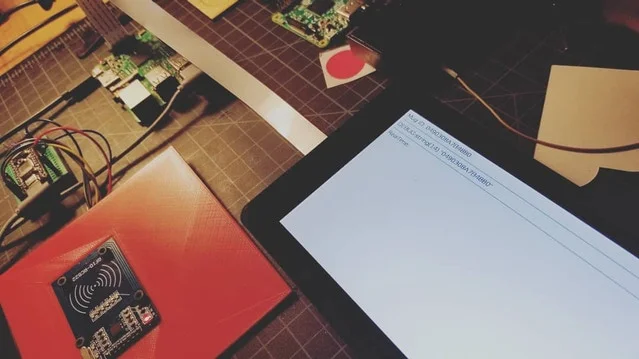
Here are a couple of pics of today's RFID dev session. First steps were finalizing the Arduino code and then integrating the data stream with Mugsy's interface.
Bits!
Mug ID to screen!
I am currently accessing the functionality from the menu so I still need to add a real time listener. Once scanned the interface redirects to a debug page displaying the mug ID info and a button to start the brewing process. Starting the brew just cycles through the relay while testing, that's the clicky clacky you're hearing and seeing. Still need to display the Brew details and actually wrap it up in the interface. #listeningto @mogwaiband
Security Deep Dive
Simplifying development is not the only reason we use standard web tech to program Mugsy. One of the greatest benefits is that the stack is constantly being audited and is battle tested every day on a worldwide scale.
But if a human makes it, a human can break it. Nothing is 100% secure. That's why I am so happy to announce that Mugsy will be the subject of a security deep dive and talk at the upcoming LASCON in late October.
Having a security expert dig into Mugsy will help us provide a better robot for all of you. It's kind of a scary prospect for me, but shining a bright light is the only way to chase out all the bugs lurking in the darkness...
I'll have more info on this in a couple of weeks so stay tuned.
Cheers,
-m